Service desk email address of a project is being leaked through graphql to non-members of the project even If a custom suffix is set for the same.
HackerOne report #1439254 by albatraoz on 2022-01-02, assigned to @cmaxim:
Report | Attachments | How To Reproduce
Report
Summary
I've reported this vulnerability previously too but closed it as N/A myself as the service desk email address is guessable If we have a project name. But this time I saw some activity on gitlab issues about the visibility & it has been changed to reporter & also If any project owner decides to add suffix to their service desk email address to defend the spam, that too would be exposed through graphql.
Steps to reproduce
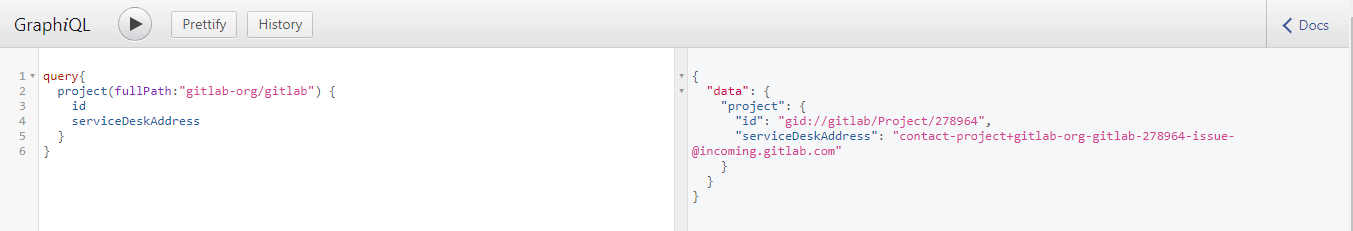
- Visit https://gitlab.com/-/graphql-explorer
- Put the following graphql query and hit play
query{
project(fullPath:"gitlab-org/gitlab") {
id
serviceDeskAddress
}
}You will see the internal service desk email of the project in the response.
{
"data": {
"project": {
"id": "gid://gitlab/Project/278964",
"serviceDeskAddress": "contact-project+gitlab-org-gitlab-278964-issue-[@]incoming.gitlab.com"
}
}
}What is the current bug behavior?
Service desk email address is visible to non members of a project.
What is the expected correct behavior?
Service desk email address should be visible only to members of a project with minium reporter level access.
Relevant logs and/or screenshots
Issue references
#345692 (closed)
!74179 (merged)
Impact reference
Impact
Even though the service desk email address is guessable If we have the project name, If the owner decides to add a secret suffix only visible & shared with project members, the email address would be leaked to non members through graphql. This can lead to issue spam or vandalism of a project.
Attachments
Warning: Attachments received through HackerOne, please exercise caution!
How To Reproduce
Please add reproducibility information to this section: