Private user email disclosure via group invitation
HackerOne report #1204320 by jimeno on 2021-05-20, assigned to GitLab Team:
Report | Attachments | How To Reproduce
Report
Summary
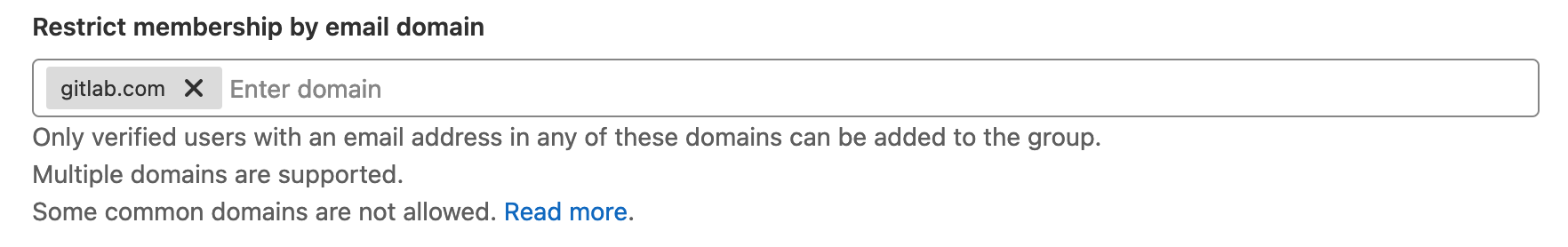
GitLab paid plans support group administrators to restrict group memberships by email domain. For example, a grpup administrator can create a setting so that all group members must have a gitlab.com email address. Related documentation can be found here.
Thanks to it, any GitLab who can create a group can leak other users email address, even when these are configured as private
Steps to reproduce
NOTE: Please, use an Ultimate GitLab instance as that's the one I used.
-
Create a GitLab group and enable domain restrictions. Only add
gitlab.comto the allow-list. -
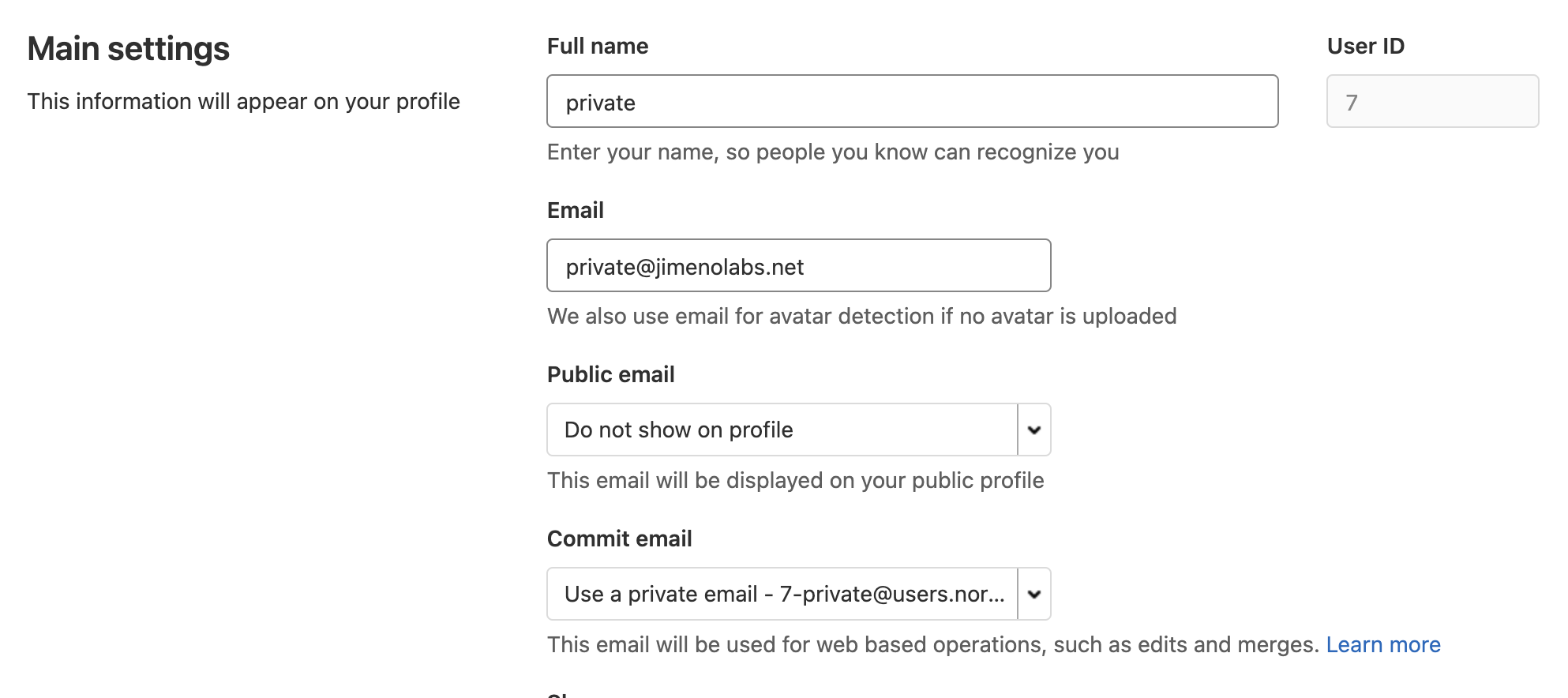
Create a new GitLab user and make sure their profile is private by following the official linked documentation.
-
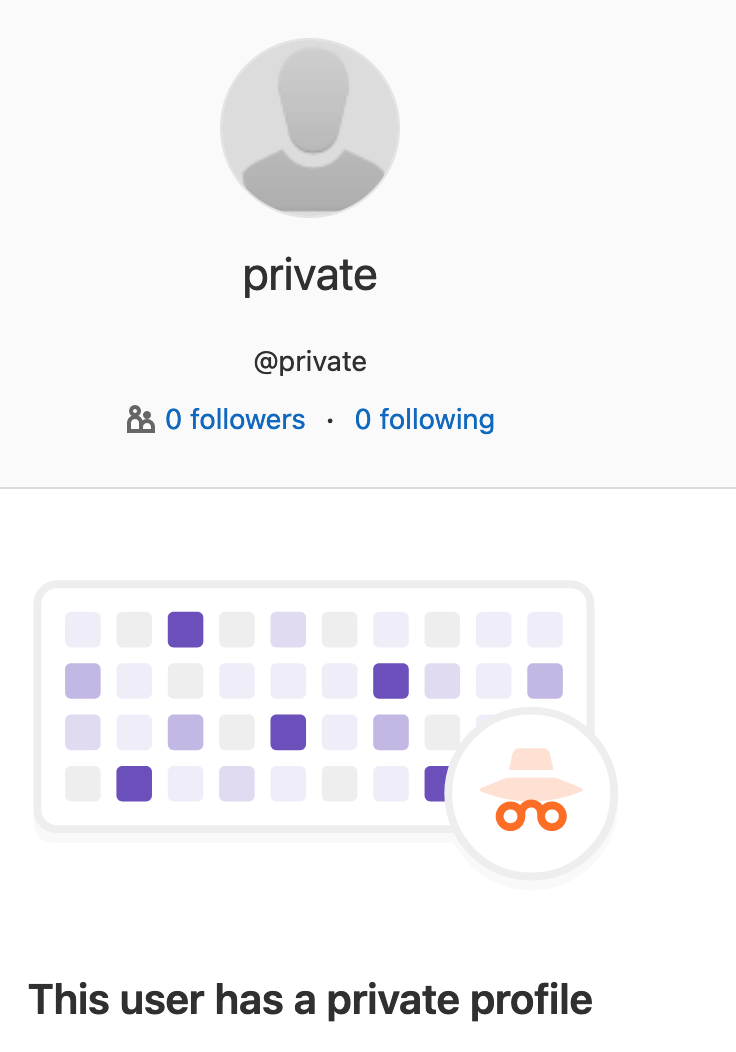
As your attacker, visit their profile
https://your-instance.tld/privateand make sure GitLab says the profile is private. -
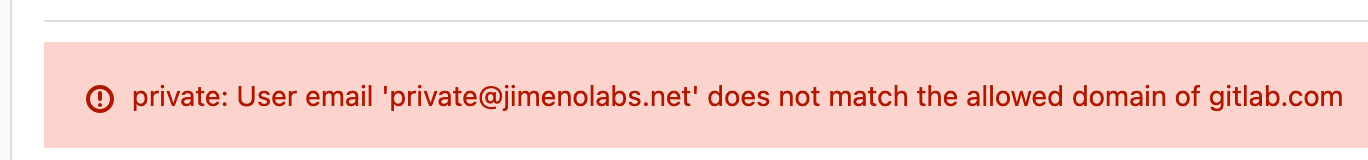
Try to invite the user to the group (you will need to know their username) and notice the error in a red textbox on top of the page displays their email address to you.
Impact
Email address disclosure.
Examples
N/A.
What is the current bug behavior?
Email address of user is displayed to attacker when group invitation fails.
What is the expected correct behavior?
Error message is displayed to the attacker while respecting invited user's privacy settings.
Relevant logs and/or screenshots
N/A.
Output of checks
N/A.
Results of GitLab environment info
root@rigel:/# gitlab-rake gitlab:env:info
System information
System:
Proxy: no
Current User: git
Using RVM: no
Ruby Version: 2.7.2p137
Gem Version: 3.1.4
Bundler Version:2.1.4
Rake Version: 13.0.3
Redis Version: 6.0.12
Git Version: 2.31.1
Sidekiq Version:5.2.9
Go Version: unknown
GitLab information
Version: 13.11.4-ee
Revision: d1a2e182d3b
Directory: /opt/gitlab/embedded/service/gitlab-rails
DB Adapter: PostgreSQL
DB Version: 12.6
URL: https://rigel.wiki
HTTP Clone URL: https://rigel.wiki/some-group/some-project.git
SSH Clone URL: git@rigel.wiki:some-group/some-project.git
Elasticsearch: no
Geo: no
Using LDAP: no
Using Omniauth: yes
Omniauth Providers: auth0
GitLab Shell
Version: 13.17.0
Repository storage paths:
- default: /var/opt/gitlab/git-data/repositories
GitLab Shell path: /opt/gitlab/embedded/service/gitlab-shell
Git: /opt/gitlab/embedded/bin/git Impact
Email address disclosure.
Attachments
Warning: Attachments received through HackerOne, please exercise caution!
- email_restriction.png
- private_view.png
- private_settings.png
- recording-1621534191673.webm
- email_disclosure.png
Proposal
A fix proposal is discussed here.