Webhook secret tokens leaked in webhook logs
HackerOne report #1757999 by joaxcar on 2022-11-01, assigned to @greg:
Report | Attachments | How To Reproduce
Report
Summary
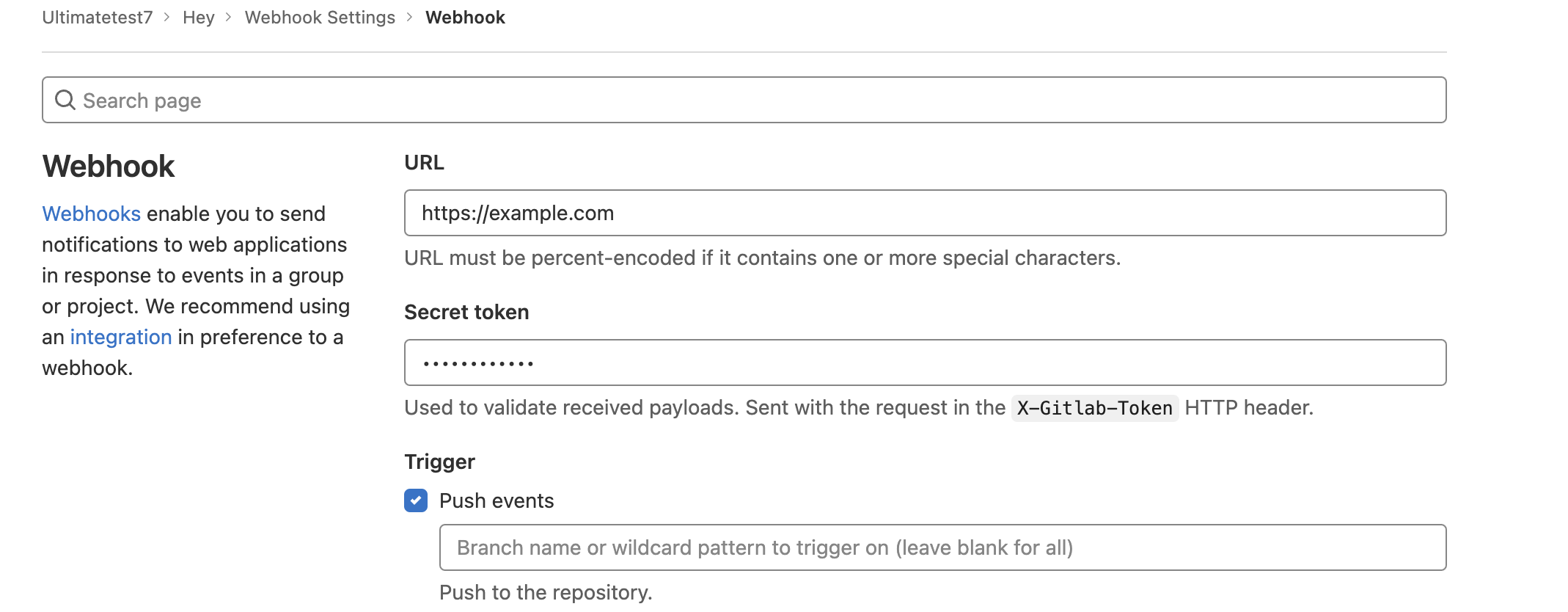
Since this issue #359989 (closed) was merged webhook secrets are hidden for maintainers of a project after they are saved. The UI and API gives no way of retrieving the secret after configuration. Just like hidden tokens in integrations. The issue states
Use type="password" for the Secret token field input. We also have to make sure that the values are not exposed to the frontend
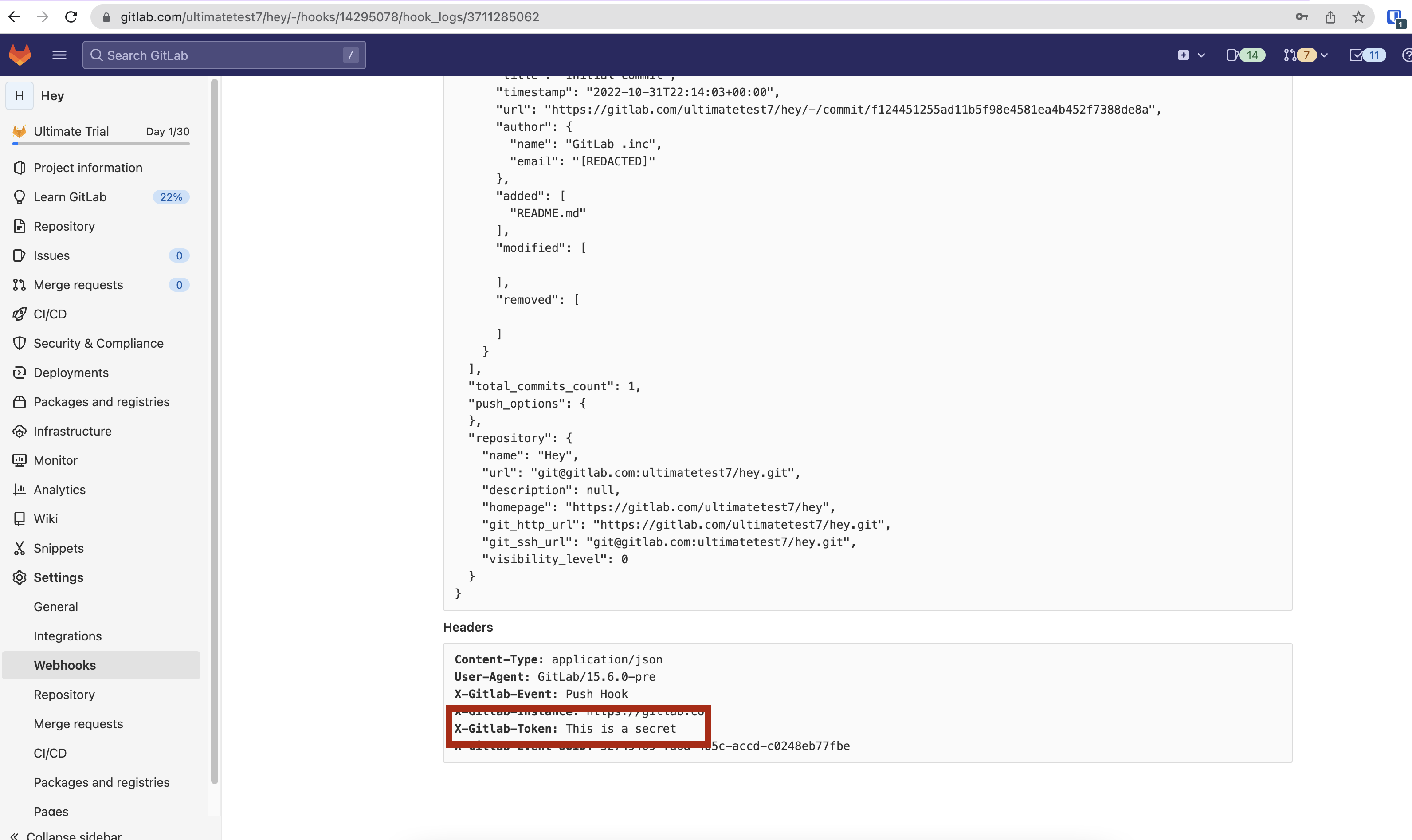
After the fix the input field only show a line of dots when trying to edit a webhook. But the webhook logs at the same page still contains the secret in plain text.
The docs states this about the secret
You can specify a secret token to validate received payloads. The token is sent with the hook request in the X-Gitlab-Token HTTP header. Your webhook endpoint can check the token to verify that the request is legitimate.
This change to the input field of the UI was made intentionally to hide the secret from other maintainers (as they do not necessarily have access to the receiving service). The leaked token (LOW confidentiality) gives an unauthorized other maintainer the ability to spoof requests to the receiving server (LOW integrity). And the impacted service is the receiving service (Scope changed). This was my rating of this, feel free to edit it as see fit!
Steps to reproduce
- Log in to gitlab
- Create a new project
- Go to https://gitlab.com/GROUP/PROJECT/-/hooks and configure a webhook. Make sure to add a secret
- Click save
- Scroll to the bottom of the page to the list of configured hooks.
- Click edit on the new hook
- You can now see that the secret is hidden
- Scroll down and click "test", a test call will be made to the hook
- Bellow the hook info there should now be a log entry, click the log entry
- Scroll to the bottom of the log page to the request headers, there is the secret in plain text
Impact
The UI leaks secret tokens that should not be accessible after configuration
What is the current bug behavior?
Secret token headers are shown in webhook logs
What is the expected correct behavior?
The secret token header should be redacted in the logs
Relevant logs and/or screenshots
Output of checks
This bug happens on GitLab.com
Impact
The UI leaks secret tokens that should not be accessible after configuration, allowing unauthorised maintainers to use the token
Attachments
Warning: Attachments received through HackerOne, please exercise caution!
How To Reproduce
Please add reproducibility information to this section: