Non- members can resolve/unresolved discussions from public projects
HackerOne report #578057 by ashish_r_padelkar on 2019-05-12, assigned to estrike:
Summary
Hello,
As per this article https://docs.gitlab.com/ee/user/discussions/#resolvable-comments-and-discussions ,
They can then be individually resolved by anyone with at least Developer access to the project or by the author of the change being reviewed.
This is true and they can resolve/unresolved all discussions individually. However, the user with no permissions to public projects can resolve/unresolved their own reply too!.
The problem with this is , if all the other comments/replies from the discussion thread is resolved , non members can simply change the whole discussions status to resolve/unresolved by simply posting a reply on discussions!
Steps to reproduce
- Create any discussion thread in merge difference on public projects merge requests.
- Now mark all the replies from this thread to resolved. This will eventually mark the discussion thread as Resolved too!
-
Now as any non member, simply post a reply on this thread. The reply will automatically posted as
Resolvedas discussion is resolved already! -
However, he can now just use this resolve/unresolved button to change the status of his own reply. Just click on green check
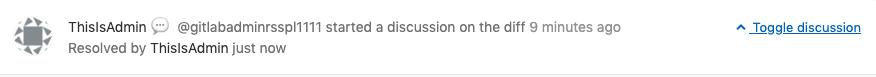
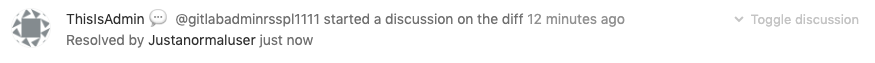
- On changing the status of his own reply, the whole discussion threads status changed as well! and the thread appears like below and resolved by username who is not a member of the project!
What is the current bug behavior?
Non- members can resolve/unresolved discussions from public projects
What is the expected correct behavior?
Only developer or author of the change should be allowed to change the statuses as mentioned in the article
Output of checks
This bug happens on GitLab.com and should also happen on omnibus installations too!
Suggested Fix
Guest/ reporter/non members should-not be allowed to resolve their own replies Also
Regards,
Ashish
Impact
Non members can resolve/unresolved discussions from public projects
Attachments
Warning: Attachments received through HackerOne, please exercise caution!