Stored XSS via KaTeX
HackerOne report #448970 by jouko on 2018-11-23:
Summary:
User-editable Markdown is used a lot on GitLab. Normally hyperlinks are checked for safety. javascript: links are rejected because malicious scripts could be executed if someone clicks on such a link.
The KaTeX library used to render math in Markdown documents however has its own linking syntax without such safety checking. This syntax may be used to inject malicious JavaScript in GitLab's Markdown.
Description: The link syntax can be found in the reference at https://katex.org/docs/supported.html#html
\href{https://katex.org/}{\KaTeX}Steps To Reproduce:
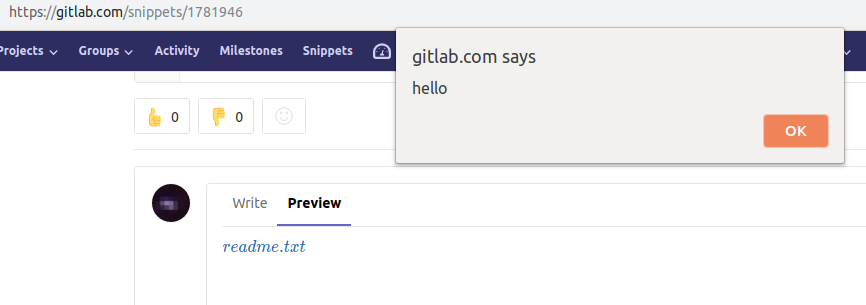
- Go to the Markdown editor, e.g. view a Snippet and enter a comment such as:
$`\href{javascript:alert('hello');}{test}`$- Click Preview to see the Markdown rendered
- Click on the link, observe the JavaScript alert box
Supporting Material/References:
Impact
The normal stored XSS impact. The victim is required to click on the link.
Attachments
Warning: Attachments received through HackerOne, please exercise caution!
Security Issue
Edited by Constance Okoghenun