Access to internal projects due to bypass of recommended email regex!
HackerOne report #498694 by bull on 2019-02-20:
Hi,
I have found an issue which can be used by an attacker to escalate privileges to an internal user on an Gitlab Enterprise Edition instance when registration is enabled and user is to be matched to regex as recommended by you in your documentation.
Issue:
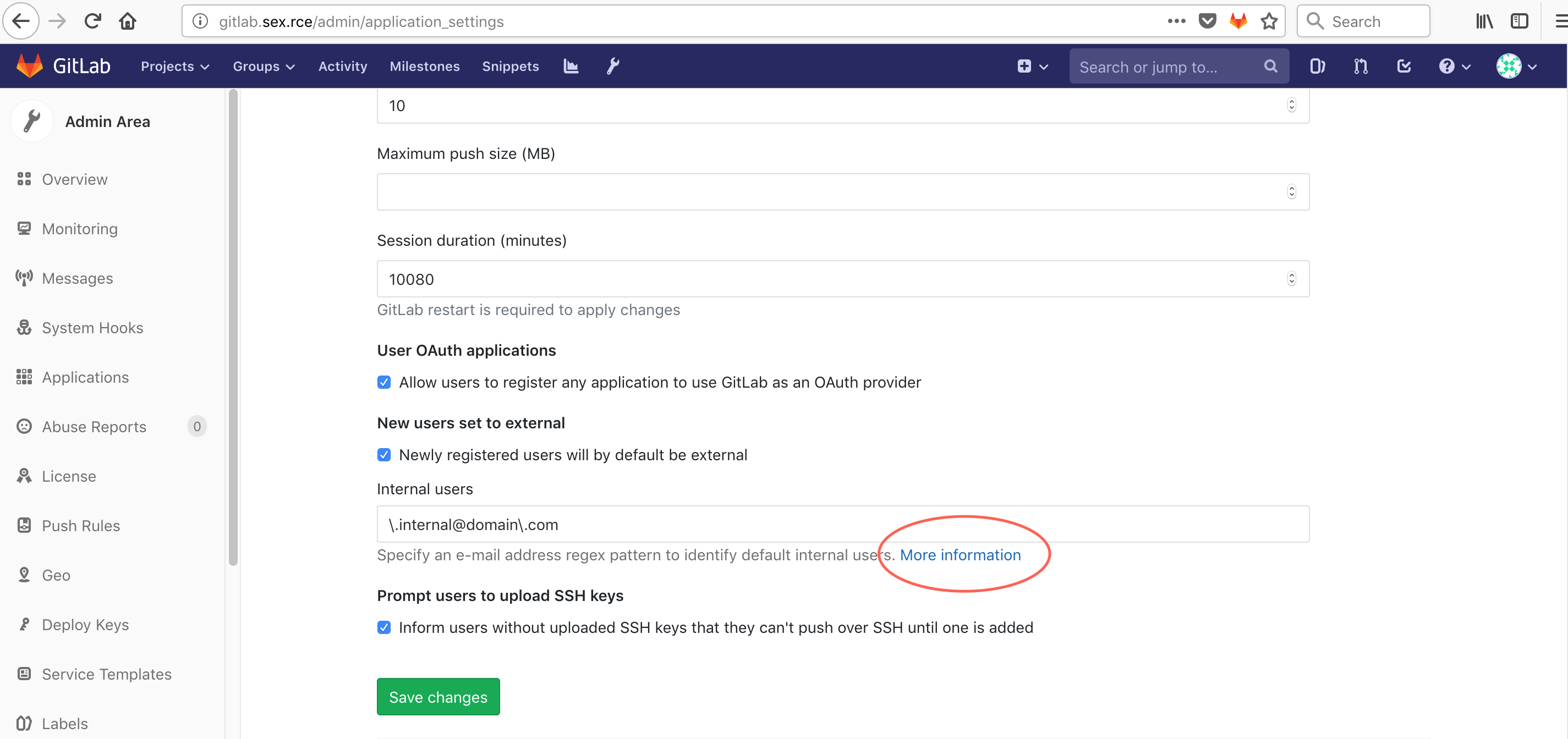
when the admin user of instance go to configure internal user, the recommendation next to the option gives a vulnerable regex check recommendation to all the admins to whitelist email with access to internal resources:
it says:
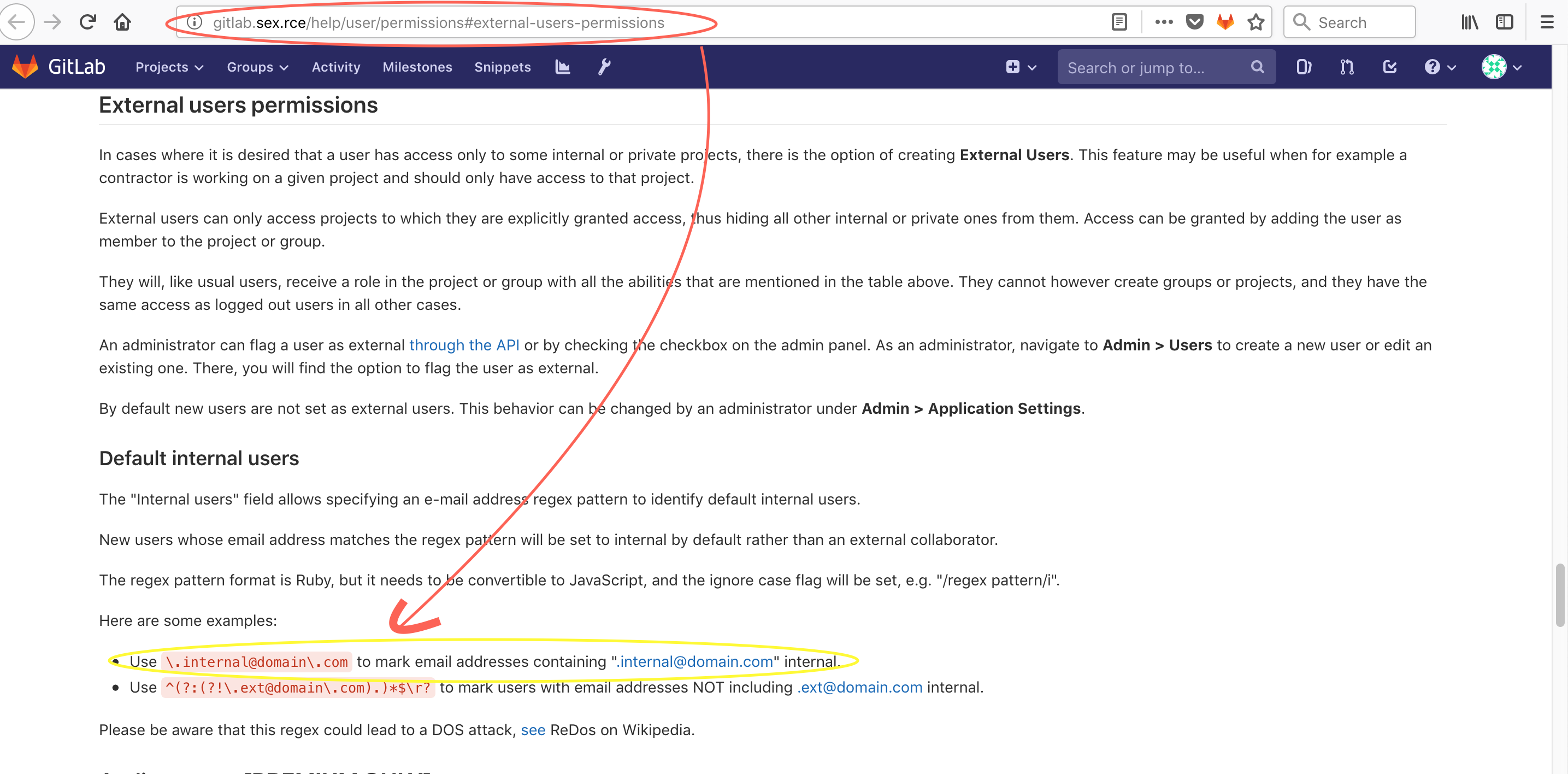
Use \.internal@domain\.com to mark email addresses containing ".internal@domain.com" internal.
This regex is vulnerable to bypass and gives extensive range of emails internal access on the instance.
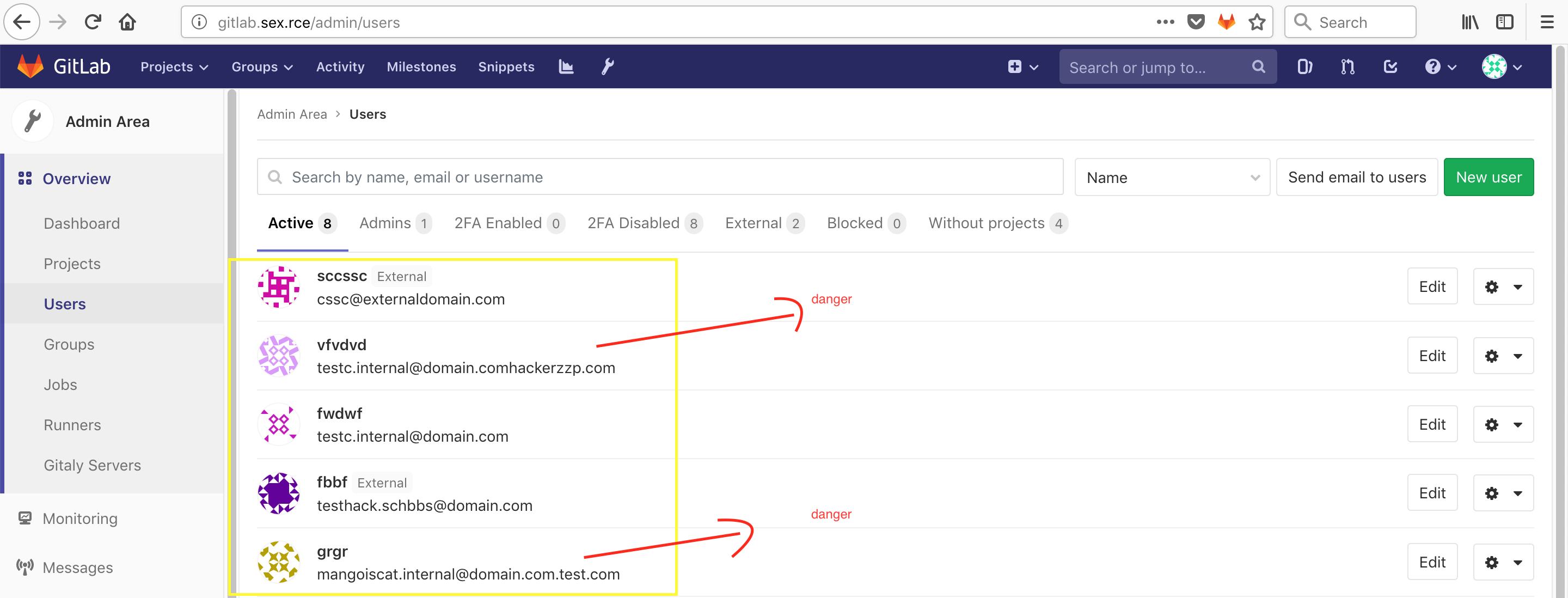
emails likes following will be considered as internal user:
anything.internal@domain.com.hackersdomain.com
anything.internal@domain.comcomhackercom.com This gives full access as an internal user i.e access to all internal projects, ability to create projects and take actions as mentioned in your docs.
Otherwise an external user donot even have access to create a project.
POC:
- on a gitlab instace login as admin and allow registered user with regex
\.internal@domain\.comto be internal.(make sure you have some internal projects to test poc) - now register with email
test.internal@domain.com.attackerdomain.comortest.internal@domain.comnewattackerdomain.comwhich you can definitely own to receive confirmation links. - login as new user and go to http://gitlab.sex.rce/explore/projects and you will see internal projects as well.
Please donot direct user to use vulnerable regex. Lots of gitlab instances are there https://www.shodan.io/search?query=%22_gitlab_session%22
Let me know if you need any more information or if i missed something.
Thanks
bull
Impact
Access to internal projects on gitlab instances
Attachments
Warning: Attachments received through HackerOne, please exercise caution!