Stored XSS in Markdown fields via Label references
HackerOne report #449191 by jouko on 2018-11-23:
Summary: A specially formatted Label reference in Markdown fields can be used to inject JavaScript on GitLab pages.
Description:
A tilde symbol followed by a double-quoted label name creates a link to the named label, i.e. ~"label name". A malicious user can enter arbitrary entity-encoded HTML in the quotes. The entities are decoded on the resulting page allowing dangerous HTML to be embedded.
Example:
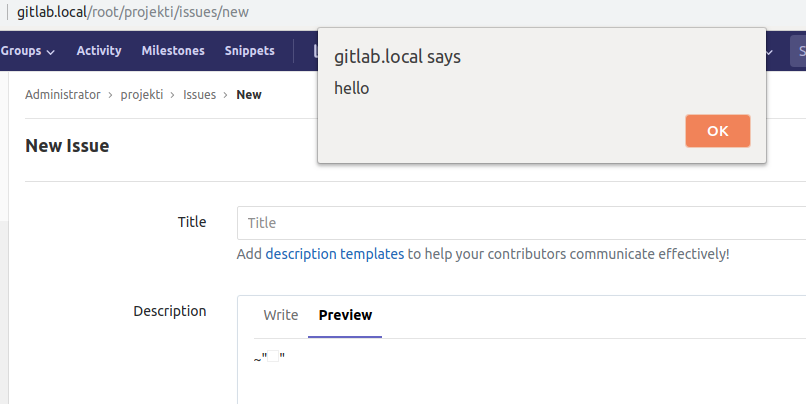
~"<img src=x onerror="alert('hello')">"Steps To Reproduce:
- Edit e.g. a README.md file of a project
- Enter
~"<img src=x onerror="alert('hello')">" - Click Preview or just save the modification
- Observe a JavaScript alert box when the page is viewed
Supporting Material/References:
Impact
An attacker could inject JavaScript in projects to compromise accounts of people who view them. See #448691 for an example of how an attacker could change the victims' SSH keys or set their passwords.
Attachments
Warning: Attachments received through HackerOne, please exercise caution!
Edited by Dennis Appelt